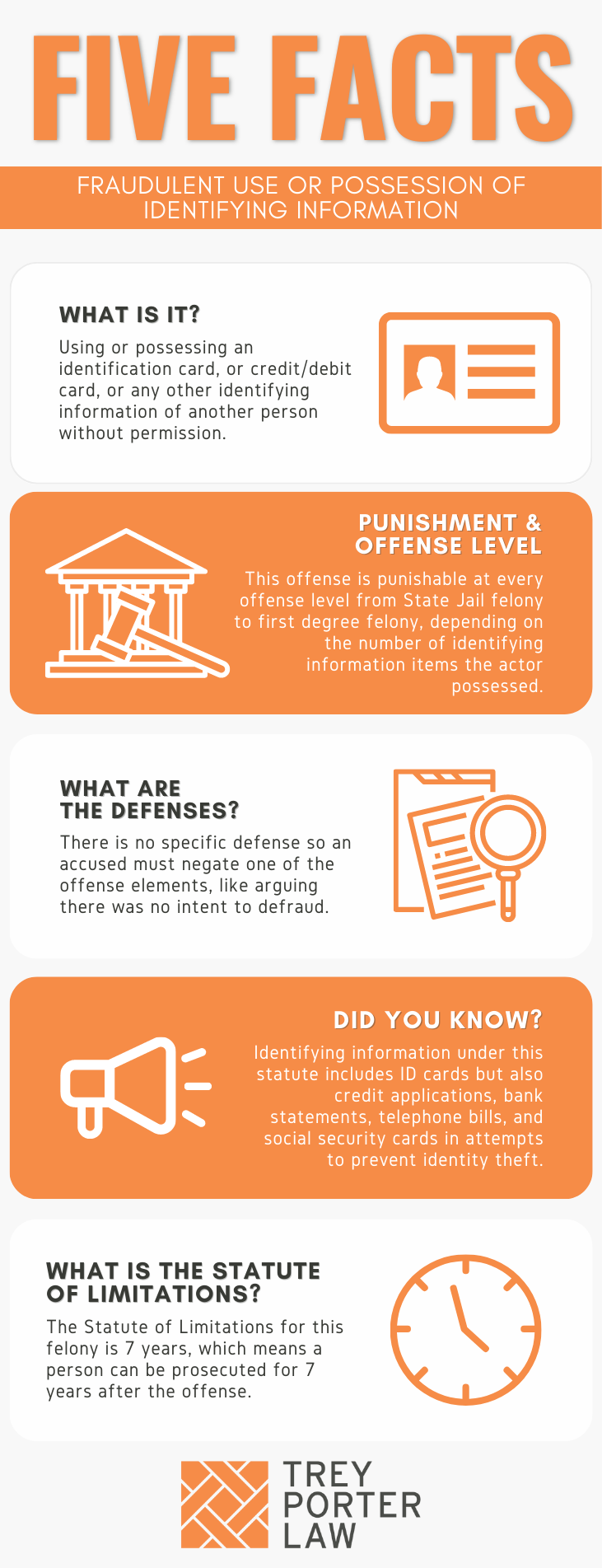
WHAT IS FRAUDULENT USE OR POSSESSION OF IDENTIFYING INFORMATION IN TEXAS?
The Texas law against fraudulent use or possession of identifying information prohibits possessing, using, or transferring another’s identification, credit card, or any other item of identifying information without permission, including a deceased person’s or a minor’s information.
- What is an “item” of identifying information? The penalties for fraudulent use or possession of identifying information depend on the number of “items” a person illegally possesses. One document, such as a license, check, or credit card, may contain many identifying items. An “item of identifying information” refers to any single piece of personal information enumerated in the statutory definition, including:
-
- a person’s name and date of birth;
- a person’s fingerprint, voice print, retina image, or other unique biometric data;
- unique electronic identification number, address, routing code, or financial institution account number;
- telecommunication identifying information or access device; or
- social security number or other government-issued identification number.
WHAT IS THE FRAUDULENT USE OR POSSESSION OF IDENTIFYING INFORMATION LAW IN TEXAS?
Tex. Penal Code § 32.51. FRAUDULENT USE OR POSSESSION OF IDENTIFYING INFORMATION.
(b) A person commits an offense if the person, with the intent to harm or defraud another, obtains, possesses, transfers, or uses an item of:
(1) identifying information of another person without the other person’s consent or effective consent;
(2) information concerning a deceased natural person, including a stillborn infant or fetus, that would be identifying information of that person were that person alive, if the item of information is obtained, possessed, transferred, or used without legal authorization; or
(3) identifying information of a child younger than 18 years of age.
(b-1) For the purposes of Subsection (b), the actor is presumed to have the intent to harm or defraud another if the actor possesses:
(1) the identifying information of three or more other persons;
(2) information described by Subsection (b)(2) concerning three or more deceased persons; or
(3) information described by Subdivision (1) or (2) concerning three or more persons or deceased persons.
(b-2) The presumption established under Subsection (b-1) does not apply to a business or other commercial entity or a government agency that is engaged in a business activity or governmental function that does not violate a penal law of this state.
(c) An offense under this section is:
(1) a state jail felony if the number of items obtained, possessed, transferred, or used is less than five;
(2) a felony of the third degree if the number of items obtained, possessed, transferred, or used is five or more but less than 10;
(3) a felony of the second degree if the number of items obtained, possessed, transferred, or used is 10 or more but less than 50; or
(4) a felony of the first degree if the number of items obtained, possessed, transferred, or used is 50 or more.
(c-1) An offense described for purposes of punishment by Subsections (c)(1)-(3) is increased to the next higher category of offense if it is shown on the trial of the offense that:
(1) the offense was committed against an elderly individual; or
(2) the actor fraudulently used identifying information with the intent to facilitate an offense under Article 62.102, Code of Criminal Procedure.
(d) If a court orders a defendant convicted of an offense under this section to make restitution to the victim of the offense, the court may order the defendant to reimburse the victim for lost income or other expenses, other than attorney’s fees, incurred as a result of the offense.
(e) If conduct that constitutes an offense under this section also constitutes an offense under any other law, the actor may be prosecuted under this section, the other law, or both.
WHAT IS THE PENALTY CLASS FOR FRAUDULENT USE OR POSSESSION OF IDENTIFYING INFORMATION IN TEXAS?
The penalty category for fraudulent use or possession of identifying information depends on the number of items in the person’s possession. If a person uses, possesses, transfers, or obtains:
- One to four items:
- State jail felony, punishable by 180 days to two years in a state jail facility;
- Five to nine items:
- Third degree felony, punishable by two to ten years in prison;
- Ten to 49 items:
- Second degree felony, punishable by two to 20 years in prison;
- 50 or more items:
- First degree felony, punishable by five to 99 years or life in prison.
If the victim is over 65 years old at the time of the offense, the penalty category and punishment range are increased to the next highest category. So, a person who possesses five to nine items of an elderly person’s identifying information will be charged with a second degree felony, rather than a third degree felony.
- Are there enhanced penalties for a registered sex offender who uses identifying information without permission during registration? Texas law increases punishment to the next highest category if the person uses another’s identifying information “with intent to facilitate an offense under Article 62.102, Code of Criminal Procedure,” which criminalizes the failure to comply with sex offender registration requirements.
WHAT IS THE PUNISHMENT RANGE FOR FRAUDULENT USE OR POSSESSION OF IDENTIFYING INFORMATION IN TEXAS?
The punishment range for fraudulent use or possession of identifying information charged as a first degree felony is five to 99 years or life in prison, and a maximum $10,000 fine. For a second degree felony, in addition to the fine of up to $10,000, the prison sentence may range from two to 20 years.
The punishment range for a third degree felony is two to ten years in prison, and a maximum fine of $10,000. Fraudulent use or possession of identifying information charged as a state jail felony carries between 180 days and two years in a state jail facility, and a maximum fine of $10,000.
WHAT ARE THE PENALTIES FOR FRAUDULENT USE OF POSSESSION OF IDENTIFYING INFORMATION IN TEXAS?
A person charged with fraudulent use or possession of identifying information may be eligible for probation after a conviction, or deferred adjudication without a conviction.
- What is the maximum length of probation for fraudulent use or possession of identifying information in Texas? A person is eligible for probation from a jury after being found guilty only if he or she has no prior felony convictions, and is sentenced to less than ten years in prison. A person who pleads guilty or nolo contendere (“no contest”) to a judge may be placed on probation at the judge’s discretion.For state jail and third degree felony fraudulent use convictions, the period of probation may range between two and five years. The probation term may not exceed ten years if the person is convicted of a second degree or first degree felony.
- What is the maximum length of deferred adjudication for fraudulent use or possession of identifying information in Texas? A person may avoid a conviction and be placed on deferred adjudication after pleading guilty or nolo contendere (“no contest”) to a judge. For a state jail felony, the deferred adjudication term will be between two and five years, with the possibility of extending it for up to ten years.For first degree, second degree, and third degree felonies, the deferred adjudication period may not exceed ten years.
WHAT ARE THE DEFENSES TO FRAUDULENT USE OR POSSESSION OF IDENTIFYING INFORMATION IN TEXAS?
In defense to a charge of fraudulent use or possession of identifying information, an accused will often assert the State failed to prove at least one of the required elements, such as the requisite “intent to harm or defraud.”
- What is “the intent to harm or defraud another”? The Texas Penal Code does not define “intent to harm or defraud,” but courts attach its plain meaning, which may be inferred from the circumstances and common sense.In Singh v. State, a defendant who was stalking a victim broke into her home. Police caught him with her mail, and computer drives. He had apparently opened an account with a credit monitoring company in her name, and was convicted of fraudulent use or possession of identifying information. The account application had the victim’s name, date of birth, address, and social security number. She testified she believed, based on her experience with the defendant, he intended to harm her, which was sufficient to uphold the conviction.
- Can the State prove a person lacked effective consent if the alleged victim does not testify? Yes, in some circumstances. Texas Penal Code Section 1.07(11) defines “consent” as “assent in fact, whether express or apparent,” based on an actual agreement or understanding. Section 1.07(19) explains consent is not effective if, among other things, it was induced by fraud, which may be inferred under the circumstances.To convict a person of fraudulent use or possession of identifying information, the State must show the person possessed, transferred, or used another’s identifying information without consent. If there is circumstantial evidence showing a person did not have consent to use another’s identifying information, that will sustain a conviction.In Grimm v. State, a defendant was caught with over 40 applications for RV rentals with the names and information of several people, personal checks, credit card statements, and utility bills of others. He also admitted he made fake IDs, and activated credit cards in other people’s names without permission. He was convicted of fraudulent possession of identifying information, which was affirmed, even though only four witnesses testified they did not give him consent. The other circumstantial evidence supported the inference that he lacked consent.
WHAT IS THE STATUTE OF LIMITATIONS FOR FRAUDULENT USE OR POSSESSION OF IDENTIFYING INFORMATION IN TEXAS?
The limitation period for fraudulent use or possession of identifying information is seven years.
FRAUDULENT USE OR POSSESSION OF IDENTIFYING INFORMATION IN TEXAS
The purpose of criminalizing the fraudulent use or possession of identifying information is to prevent identity theft. Given the elusive nature of identity theft in the digital age, which is not always tied to the possession of any tangible document, the Legislature aimed to prevent identity theft through punishing the possession or use of identifying information.
TEXAS FRAUDULENT USE OR POSSESSION OF IDENTIFYING INFORMATION COURT CASES
The case law regarding fraudulent use or possession of identifying information in Texas illustrates the various acts constituting a violation of this statute.
- In Ramirez-Memije v. State, the defendant received a credit card skimmer from one person, and delivered it to another in exchange for cash, who skimmed credit card numbers from customers at a restaurant before returning it to the defendant. The police caught the waiter who used the device, who then set up the defendant. When police seized the skimmer from the defendant, it contained several items of identifying information. At trial, despite the defendant’s assertion that he did not know the skimmer contained identifying information, a jury found him guilty.